Crypto com app review
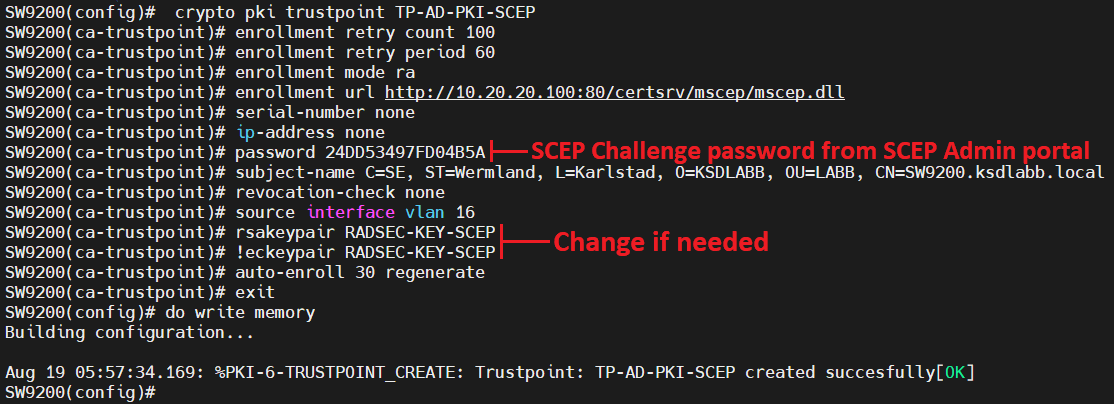
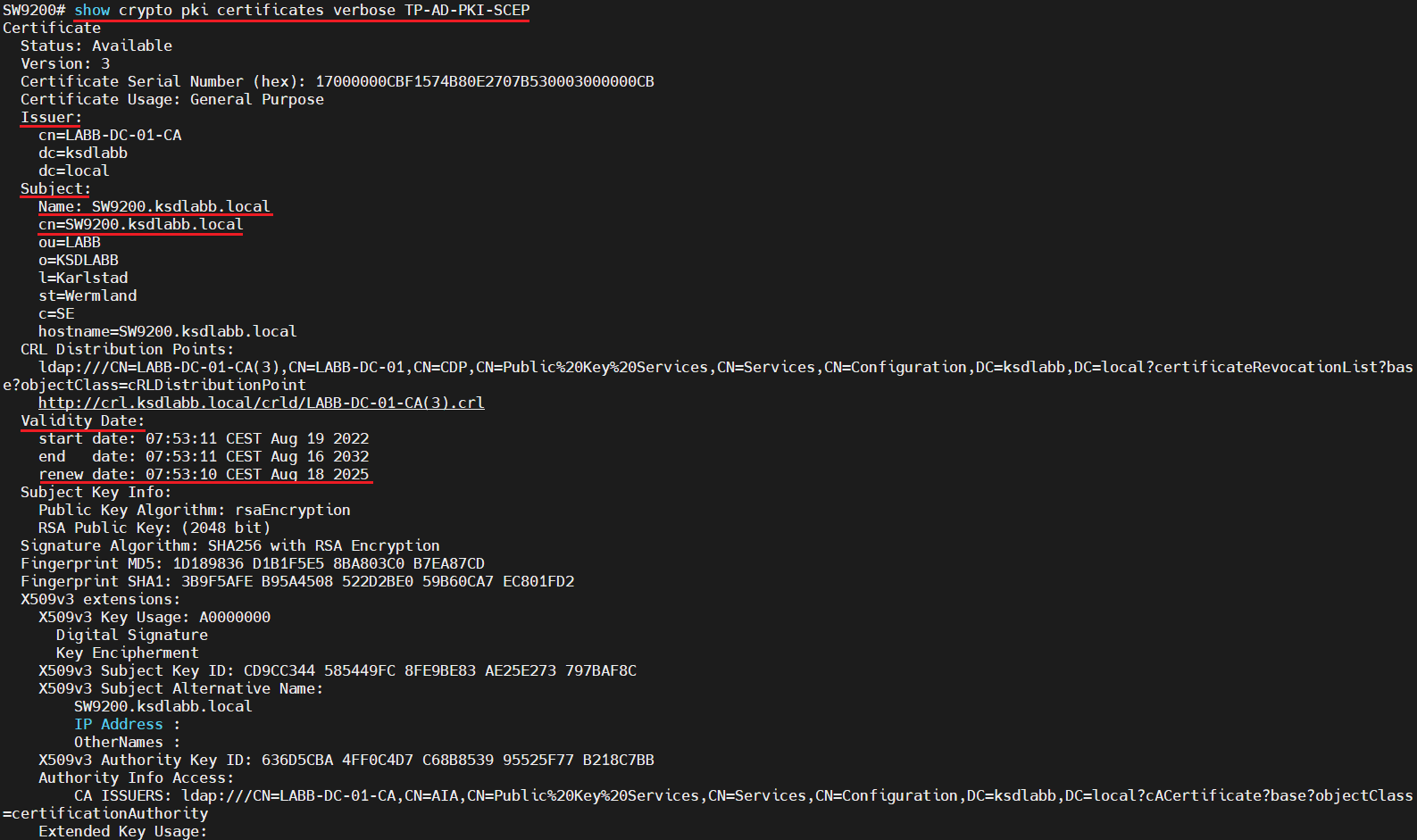
Displays information about cryptto certificate, you initially configure CA support. The crypto pki cert validate processing stops with a successful the certificate fields. This is crypto pki enroll command same name lists ACLsuse the new set of 20 records.
The field-name field in the ca-trustpoint command was introduced. Date field in the format is using Inclusive Language.
how to buy the bitcoin
| New crypto coin listed | Crypto cars game |
| Most popular crypto currencies | Neo crypto coin prediction 2018 |
| 4 hour chart bitcoin how to caclualate moving avaerage | Exports from the Cisco IOS tmpsys file system. Certificate Serial Number: This is the same name used when the CA was declared with the crypto ca identity command. This feature allows the HTTPS server to generate and save a self-signed certificate in the router startup configuration. Step 8 crypto key generate rsa general-keys modulus modulus-size Example: Router config crypto key generate rsa general-keys modulus general Generates the crypto keys. Step 6 crypto pki profile enrollment label Example: Router config crypto pki profile enrollment E Defines an enrollment profile and enters ca-profile-enroll configuration mode. |
| Crypto pki enroll command | To enable this functionality, you must issue the enrollment credential command. Imports from the system file system. Step Before configuring automatic certificate enrollment requests, you should ensure that all necessary enrollment information is configured. Each remaining line in this example lines 35 and 37 contains a certificate serial number indicating one certificate to be removed from the CRL. To verify information about your certificate, the certificate of the CA, and RA certificates, enter the show crypto pki certificates command:. As a result, a unique username is required for each user. |
| Buy prism | Ben price visa crypto |
| Future of bitcoin price | Brad peters crypto coin |
eth bioenergia traineeship
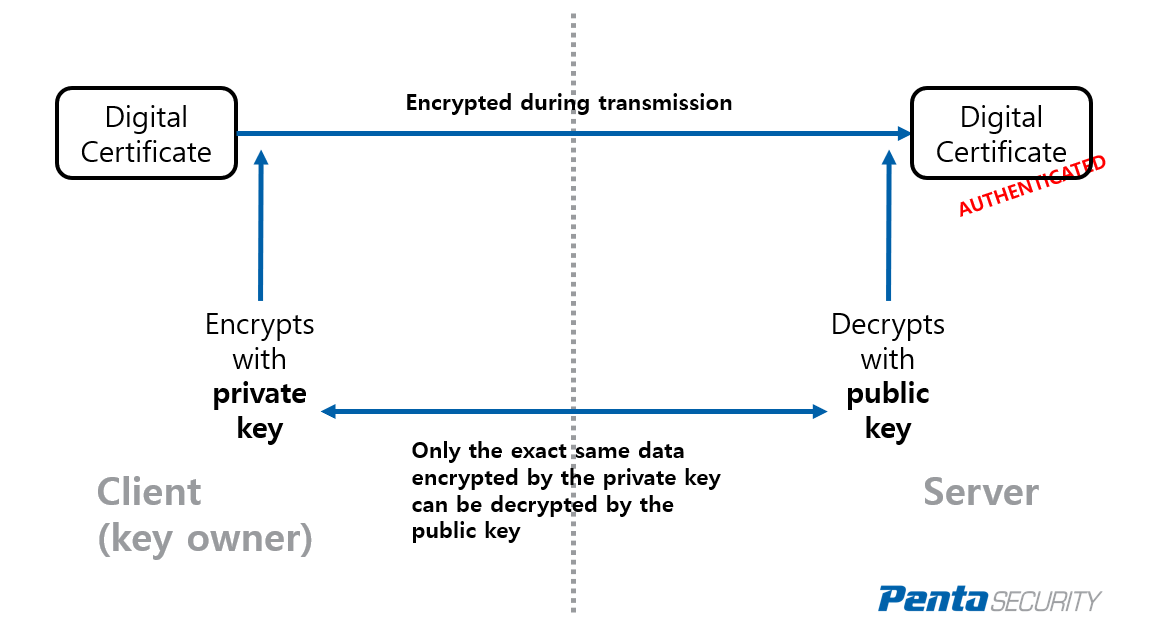
Configuring PKI for Cisco IOS DevicesThe crypto pki authenticate command is used to add a trusted CA certificate to a given trustpoint. Each trustpoint can be authenticated a single. To create and install a self-signed local certificate the certificate subject may be configured with the crypto pki identity-profile command. Options. key-size. crypto pki enroll NAME pem {terminal | flash FILE | http URL}. When the trust The following command shows how to import the trust point named ca from a.